PCI DSS compliance validation – What it means to be a Level 2 merchant
This article is a guide to help you help your merchant customers understand what it means when they become a Level 2 merchant. Many of these merchants will already be familiar with the Payment Card Industry Data Security Standard (PCI DSS) and the need to annually self-assess their compliance with that standard, often via Sysnet’s compliance portal, Sysnet.air (https://sysnetgs.com/security-compliance/) or supported by Sysnet’s Proactive Data Security Service (https://sysnetgs.com/proactive-data-security/).
Level 2 compliance validation is likely to mean those merchants will no longer use an online compliance portal to identify their SAQ type, assess and report compliance and will need to take more responsibility for ensuring they accurately scope and assess the compliance of their payment environment(s). In this article we will explore PCI DSS compliance validation for Level 2 merchants and discuss: why there are now more Level 2 merchants; where the merchant PCI DSS compliance obligation comes from; what being a Level 2 means for compliance validation and what merchants can expect when they assess compliance as a Level 2.
Contactless payment volumes surge in the wake of COVID-19
The increase in contactless payments has been one of the most significant changes in consumer behaviour resulting from the COVID-19 pandemic. According to Payments Cards & Mobile, data from Visa showed that contactless cards were used in 73 percent of all card transactions world-wide in 2020.
The shift to contactless can be seen in all countries, to a greater or lesser extent: the UK saw a 12% increase in contactless payments in 2020 to 9.6 billion, more than a quarter of all payments; while in Germany, the shift towards contactless cards has been even more pronounced with a 500% growth in transaction values between 2019 and 2021. The rise of contactless payments is also seen in the U.S. where a survey found that 67% of retailers now accepted some form of no-touch payment.
Although merchants were forced into implementing social distancing, one-way systems and screens at points of sale in order to provide a safe shopping environment, retailers have also recognised that offering hygienic, touch-free payment was another safety measure they could easily choose to make. Wary shoppers could be encouraged back into stores by retailers offering contactless payment acceptance that allowed for minimal in-store interactions, offered speedier transactions and helped to reduce queuing.
The consumer move to contactless also means fewer cash payments and many in the industry believe that this is another COVID influenced behavioural change that will not go back to ‘normal’. For example, an ECB survey reported that 87% of the respondents from Euro area countries who paid less in cash during the pandemic would continue to do so when the crisis is over. This is supported by the findings of Visa’s Back to Business Study:
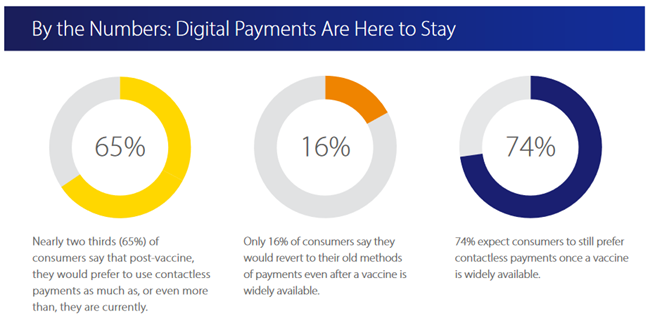
With many more merchants able to accept contactless payments and many consumers willing and wanting to pay using their contactless cards rather than cash, you may now be informing many more of your merchant customers they are a Level 2 merchant for their PCI DSS compliance validation. As cash payments are replaced by large numbers of low value contactless payment transactions, more merchants are reaching the 1 million annual transactions threshold that requires Level 2 compliance reporting.
The merchant PCI DSS compliance obligation
PCI DSS provides a set of technical and operational requirements designed to protect payment card data
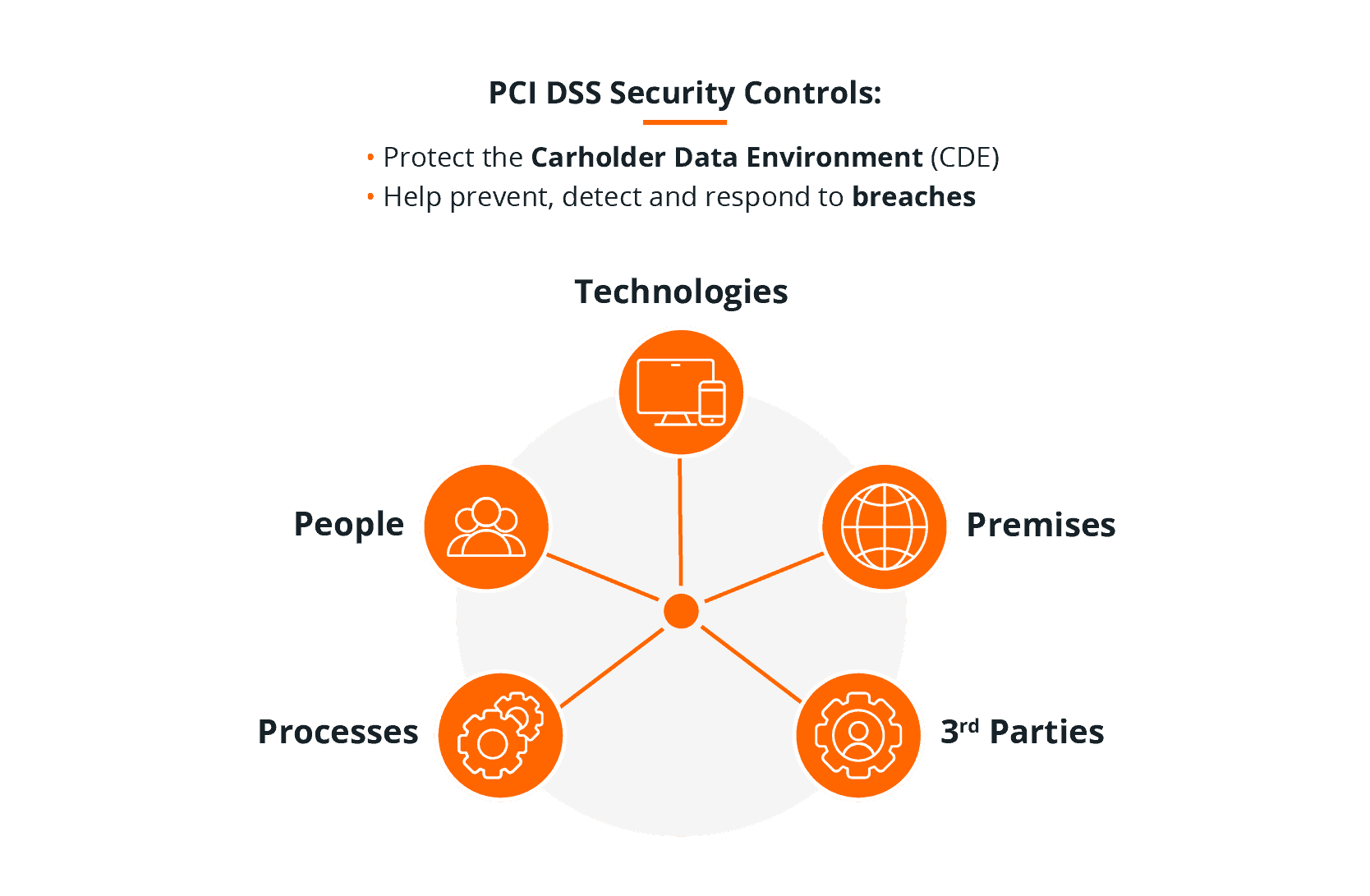
All entities that store, process or transmit payment card data – including merchants accepting card payments from customers – are expected to comply with the PCI DSS in order to properly protect the payment card data they accept or capture in their environments, that they transmit or process through their systems, or store physically in their environment or electronically in their systems.
Some entities are also expected to validate their PCI DSS compliance – that is not just saying that they comply but actually verifying and demonstrating their compliant status against the PCI DSS requirements.
The requirement to validate PCI DSS compliance is entirely separate from the obligation to comply with the requirements of the PCI DSS.
Merchants are required to validate their PCI DSS compliance annually. That annual PCI DSS compliance validation requirement comes from this flow of relationships:
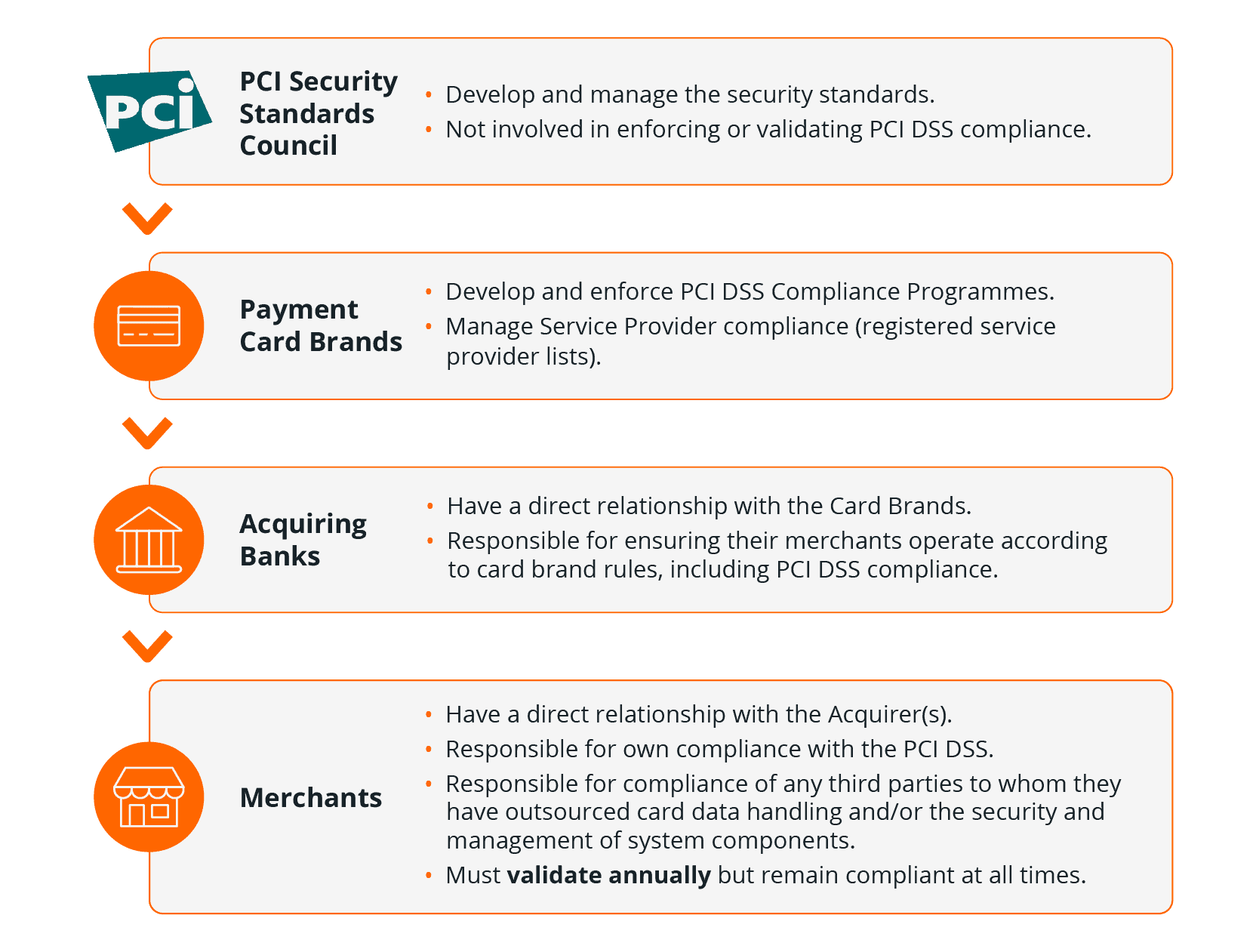
Each payment card brand has defined their own PCI DSS Compliance Programme. Those programmes require validation of compliance only for merchants and for service providers.
The acquiring banks are responsible for making sure their merchants operate according to the payment card brands’ rules, including complying with the PCI DSS. They are therefore obliged to require annual validation of compliance from their merchant customers and set out this obligation in their merchant services contracts.
What being a Level 2 means for PCI DSS compliance validation
The payment card brands’ PCI DSS Compliance Programmes specify compliance validation reporting requirements for different categories (or levels) of merchant.
Each card brands’ compliance programme defines up to four different levels of merchant, where each level is based on an annual volume of transactions and, in some cases, the payment channel. Be aware also that Mastercard defines a merchant’s level based on either their Mastercard transaction volume or because the merchant meets Visa’s criteria for that level.
The summary table of the four levels, below, shows that Level 1 merchants must always engage a PCI Qualified Security Assessor (a QSA) to perform an on-site assessment of PCI DSS compliance – producing a Report on Compliance using the PCI Council’s template. While all other merchant levels are able to self-assess their PCI DSS compliance – using the appropriate PCI DSS Self-Assessment Questionnaire (SAQ).
Level 1 | Level 2 | Level 3 & 4 | |
Type of Assessment | On-site Assessment (by QSA) | Self-Assessment (by ISA*) | Self-Assessment |
Reporting Requirement | Report on Compliance (ROC) | Self-Assessment Questionnaire (SAQ) Attestation of Compliance (AOC) | Self-Assessment Questionnaire (SAQ) Attestation of Compliance (AOC) |
Each merchant’s level is determined by their acquiring bank – the entity that sees the volume of transactions being processed by that merchant. Multi-acquired merchants with multiple payment channels could be considered a Level 4 merchant by one acquirer and a Level 2 with another and would be able to validation compliance through annual Self-Assessment questionnaire to each acquirer, even though overall their aggregate volume of transactions may make them a Level 1. Such merchants may then choose to engage a QSA and assess compliance through on-site assessment and completion of a Report on Compliance to provide themselves with greater confidence in their compliance with the PCI DSS.
It is only when the detail of the payment card brands programmes is explored that the difference in Level 2 compliance validation becomes clear:
Level 1 | Visa transactions annually | Mastercard transactions annually | American Express transactions annually | Discover transactions annually | JCB transactions annually | Compliance |
4 | E-commerce merchants only: Less than 20,000 Visa e-commerce; | All other Mastercard merchants | 10,000 or less | - | - | Self Assessment Questionnaire (SAQ) Quarterly ASV Scan (if applicable) American Express: validation optional unless required in brand discretion Mastercard: validation in Acquirer discretion |
3 | 20,000 to 1 million | More than 20,000 e-commerce; less than or equal to one million total combined Mastercard (or Visa) | 10,000 to 50,000 | All other merchants | - | Self Assessment Questionnaire (SAQ) Quarterly ASV Scan (if applicable) American Express, Discover: validation optional unless required in brand discretion |
2 | 1 to 6 million (across all channels) | 1 to 6 million Mastercard (or Visa) | 50,000 to 2.5 million | 1 to 6 million Discover | Less than 1 million | Self Assessment Questionnaire (SAQ) Quarterly ASV Scan (if applicable) Mastercard only: if completing SAQ A, A-EP or D must engage ISA or QSA |
1 | Over 6 million Visa (across all channels) | Over 6 million Mastercard (or Visa) OR, any compromised merchant OR, in Mastercard’s sole discretion | 2.5 million or more | Over 6 million Discover OR, in Discover’s sole discretion OR, Level 1 with another card brand or Acquirer | 1 million or more AND, all Internet Payment Service Providers (IPSP) | Formal On-Site Assessment with completed Report on Compliance (ROC) Quarterly external network scan by an Approved Scan Vendor (ASV) (if applicable) |
As consumer usage of contactless payments has gradually grown and then accelerated in response to COVID, many more merchants are reaching Level 2 transaction volumes – because each tap is a transaction that contributes to the merchant level.
As the table above shows, although all Level 2 merchants can validate compliance annually through self-assessment, Mastercard has added conditions:
Level 2 merchants completing SAQ A, A-EP or D are required to engage a QSA or Internal Security Assessor (ISA) for annual compliance validation.
However, Mastercard now considers (as of March 2021) Level 2 merchants completing SAQ B, B-IP, C-VT, C or P2PE to be a lower security risk and these merchants may still self-assess – as they did as a Level 4 or 3 merchant – without any requirement to engage a QSA or ISA. Optionally, Level 2 merchants may still choose to engage a QSA or ISA to complete an on-site assessment and Report on Compliance instead of self-assessing.
Mastercard Level 2 merchant compliance validation
Mastercard requires SAQ A, A-EP or D merchants to engage their own ISA or external QSA to complete the assessment to give them greater confidence in the Level 2 merchants’ compliant status.
However:
-
They are higher security risk merchants with more complex payment acceptance environments and/or are ecommerce merchants; a card data breach may be more likely
-
Of the significant volume of transactions being processed (over 1 million per annum); the potential impact would be much greater in the event of a card data breach (in terms of the volume of compromised cards and therefore the cost and potential for card fraud)
Engaging PCI trained personnel to complete the assessment and validate the Level 2 merchant’s compliance, will provide greater assurance of the merchant’s compliant status, as this should mean:
-
The assessment has been scoped accurately;
-
The assessment completed correctly
If the Level 2 merchant does not have an ISA working for them and/or wants to save on the annual cost maintaining their own ISA, they can engage a QSA. To meet Mastercard’s requirements at a minimum the QSA must perform the self-assessment of compliance on the merchant’s behalf. This means that the QSA will carry out the required testing procedures for the applicable SAQ(s) but instead of their assessment resulting in a Report on Compliance (ROC), the QSA will complete the SAQ(s) including Part 3c. of the associated Attestation(s) of Compliance, the ‘Qualified Security Assessor (QSA) Acknowledgement’.
Optionally, the merchant could choose for the QSA to perform a full on-site assessment of compliance – as they would for a Level 1 merchant – resulting in the Report on Compliance (a ROC).
What to expect when assessing compliance as a Level 2
The first step for the Level 2 merchant’s assessment is confirming the assessment scope and validating their SAQ eligibility. This can often be the first time the merchant has utilised PCI trained personnel to review, in detail, their payment methods, payment channels, networks and systems. The ISA or QSA may find that the merchant’s assessment scope is not what they thought – there are actually more people, processes, technologies in scope for PCI DSS than the merchant knew or expected.
This is often because when self-assessing, many merchants don’t realise or appreciate the true nature of PCI DSS applicability and scoping:
-
That in-scope systems include all computers or mobile devices, applications, systems and networks that store, process, or transmit payment card data;
-
As well as those systems that share the same network – even if they don’t in themselves store, process, or transmit card data;
-
In addition, the merchant’s scope needs to include systems that maybe outside of the defined cardholder data environment (the CDE) but which can connect into (or access) systems in the CDE.
The PCI SSC’s Guidance for PCI DSS Scoping and Network Segmentation Guidance for PCI DSS Scoping and Network Segmentation gives a more detailed explanation of the systems that are not CDE systems but must still be considered in scope for PCI DSS because they are connected-to or security-impacting systems.
That initial review of merchant scope can mean that some Level 2 merchants may find that they are not truly eligible for the SAQs they were self-assessing against as a Level 4 or Level 3 merchant. All of the smaller SAQs – those SAQ types that apply to particular payment processing methods, such as processing via Virtual Terminals or using standalone card terminals – include criteria that state only system types defined in the SAQ’s eligibility criteria may be used in the environment. The defined system type (for example, the standalone terminal) must not be connected to any other systems.
This is explained in PCI SSC FAQ 1443 What is the intent of the SAQ eligibility criteria? Which confirms that ‘each SAQ defines specific criteria that must be met in order to be eligible to use that SAQ’ which means that the merchant environment must be properly scoped to ensure it is ‘suitable for validation against the subset of PCI DSS requirements contained in [a particular] SAQ’.
Level 2 merchants may therefore find that they have additional PCI DSS requirements to implement and new people, processes, places and systems to apply them to. This may sound like all Level 2 merchants’ PCI DSS compliance assessments will be a lot harder – but that’s not necessarily the case. If the merchant completed an SAQ B for their face to face payments using dial-up terminals, or an SAQ A for their ecommerce website that redirects to a hosted payment page, it is very likely that the same SAQ will apply now that they are a Level 2.
Opportunities for scope reduction
Even if it is the case that the merchant is not eligible for the SAQ they thought they were, their assessor will be able to advise on what remediation is needed, where they can implement controls to segment networks/systems and reduce scope to achieve their intended SAQ eligibility. The merchant, with their assessor, can also explore options that could simplify their compliance and self-assessment requirements.
In this Virtual Terminal example shown below, there’s just a single PC on the corporate network being used to enter card payments:
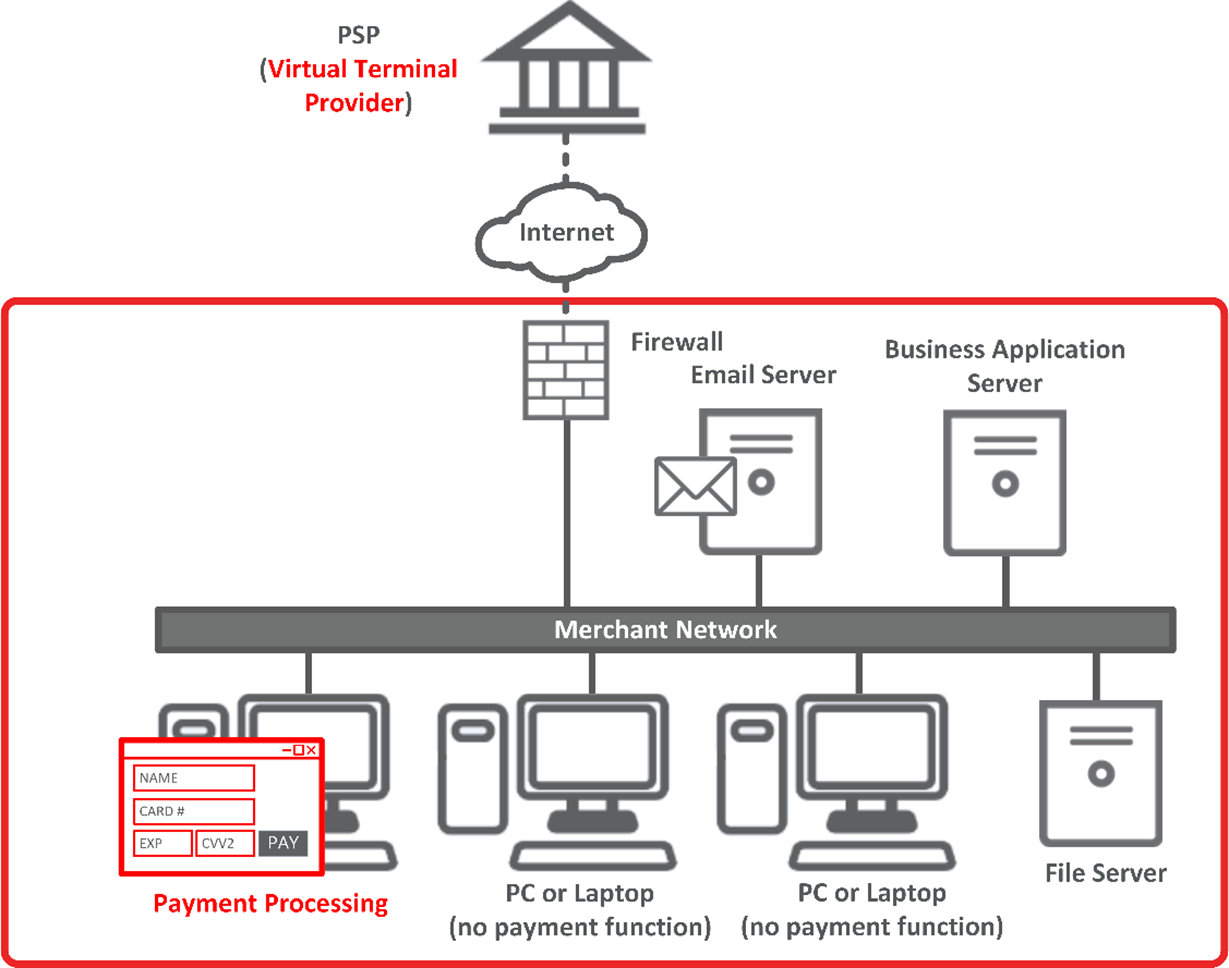
But that single PC brings all the other systems sharing that same network it into scope for PCI DSS and negates the merchant’s eligibility for the SAQ C-VT. It may also be that IP telephony is being used to take the payment card details over the phone – that transmission of card data over another IP networks can also impact on SAQ eligibility – as the SAQ C-VT also specifies ‘Your company does not otherwise receive or transmit cardholder data electronically through any channels (for example, via an internal network or the Internet).
In this scenario, there are a number of options then open to the merchant – and this is where engaging a QSA can be beneficial as they are likely to have a broader awareness and experience of the different approaches and solutions available than an ISA. For this example, options include:
-
Network segmentation, isolate the PC or tablet being used to take payments via the VT
-
If IP telephony or call recording is an issue, the merchant could change to a dedicated phone line or mobile phone call
-
Use of a Pay By Link solution so that the merchant only takes the order details over the phone but then generates and sends a secure payment link via email, text or social media chat to the customer, who then pays online (the payment page is hosted by a PCI DSS compliant service provider)
-
Outsource the telephone payment, e.g.
-
To a PCI DSS compliant third-party call centre
-
To a PCI DSS compliant provider of IVR/Automated telephone payment solutions – which could also allow the merchant to accept payment calls 24/7
-
To one of the many hosted DTMF-based solutions provided by PCI DSS compliant service providers. These can offer both attended (agent assisted) and unattended telephone payments, where card data is entered by the customers using their telephone keypad. The merchant’s call handlers, computers, systems and networks no longer come into contact with card data.
External vulnerability scans
If the merchant’s SAQ type requires the completion of quarterly external vulnerability scans undertaken by a PCI Approved Scanning Vendor (ASV), they will likely have been utilising the ASV scan management tool offered by their acquirer’s PCI DSS compliance portal to perform those scans.
Level 2 merchants typically submit their compliance validation documentation directly to their acquirer’s compliance management team and therefore may no longer have access to the acquirer’s PCI DSS compliance portal and hence to the ASV scan management tool.
These merchants will need to engage their own Approved Scanning Vendor (if ASV scans are needed for their self-assessment) and may need to use the PCI SSC’s ASV listing to identify a suitable provider: https://www.pcisecuritystandards.org/assessors_and_solutions/approved_scanning_vendors
That in itself may be an opportunity. For example, the merchant could choose to engage an ASV that also is a specialist in web application security assessments and penetration testing able to provide a comprehensive vulnerability assessment service. Such additional assessment or testing may not be explicitly required for their PCI DSS compliance but would benefit the merchant by identifying attack vectors, finding weaknesses in their defences and thereby improving their overall security posture.
Other opportunities and benefits of being a Level 2 merchant
Having PCI trained personnel involved in a Level 2 merchant’s PCI DSS compliance efforts can greatly benefit a merchant business. With the support of a qualified assessor’s greater knowledge of the PCI DSS and of payment solutions, Level 2 merchants may find that they can make PCI work better for them. They may also find that by working with an assessor and engaging directly with their acquirer’s compliance management team, they have greater flexibility in the approach to their compliance assessment and validation.
Many acquirers require merchants to attest at the company or group level through their compliance management portals, i.e. completing one self-assessment and one Attestation of Compliance for all of their payment card activities. For multi-outlet, multi-channel merchants, eligible for multiple individual SAQ types for each of their payment methods, that can mean that their assessment is a composite SAQ D – made up of the assessment questions from each SAQ type. For example, a merchant with multiple payment channels individually eligible for particular SAQs, such as the SAQ A for their ecommerce channel and SAQ B-IP for their face to face channel, would face a single set of questions from the combination of SAQ A and B-IP and attest only once, after all questions in that SAQ D composite are answered in the affirmative.
Compliance reporting flexibility may be available for Level 2 merchants that have multiple payment channels or payment methods individually eligible for particular SAQs. Using the same example, the merchant could assess and attest compliance for their ecommerce channel against SAQ A for the ecommerce channel and an SAQ B-IP for their face to face channel. These SAQs could be completed and submitted separately to their acquirer – assuming each SAQ’s eligibility criteria are being met and this approach is accepted by their acquirer.
Although merchants taking this approach won’t be considered fully compliant at the company or group level until all of their payment channels are validated as compliant (as their compliance is reported to the brands at that level), a channel by channel approach can be easier for the merchant to manage. Often different teams are involved in or support different payment channels; implementing and assessing compliance for each channel may be the responsibility of entirely different personnel. It can allow merchants to validate partial compliance, even as they work on remediating their more difficult or complex payment channels. This ability to demonstrate progress towards full compliance can be beneficial both internally, to senior or executive management sponsoring compliance efforts, and externally, to acquirers keen to be assured of the merchant’s commitment to and roadmap for PCI DSS compliance. It is an approach that can stand the merchant in good stead should a card data breach occur.
Lastly, a Level 2 merchant may find that ongoing maintenance of their PCI DSS compliance becomes easier. That’s because in order to satisfy their assessor and validate compliance they may have made technology changes or reduced their assessment scope, may now have more robust business-as-usual compliant processes in place, and PCI DSS awareness across the company may now be higher.
Greater assurance of compliance
With the additional effort that is needed to make sure:
-
The merchant is assessing the correct scope;
-
That all the applicable people, processes and technologies have been assessed;
-
And that the merchant can prove to a PCI qualified assessor (ISA or QSA) that they are compliant;
the merchant, their acquirer and the card brands have much greater assurance of the company’s compliance and hence of the security of the card data they handle.
This is particularly important in light of company obligations with regards to the protection of personal data. Data protection legislation across the globe, including the EU’s General Data Protection Regulation (GDPR), U.S. federal and state laws and regulations data protection, include those elements of payment card data that could be used to identify an individual in their definitions of personal data. These laws and regulations expect companies to have appropriate technical, physical and organisational measures in place to protect the security of personal data. For payment card data this means implementing the applicable controls required by the PCI DSS as it is the industry standard expected of all entities involved in payment card processing. For example, the UK’s Information Commissioner explicitly states that: if you process card data and suffer a personal data breach, the ICO will consider the extent to which you have put in place measures that PCI DSS requires, particularly if the breach related to a lack of a particular control or process mandated by the standard.”. Therefore, businesses that are PCI DSS compliant are also protecting themselves from the risk of the severest fines that could be levied by data protection authorities in the event of a payment card data breach.

